 In this case they focused on the last-level cache, a form of memory that saves processing time by temporarily storing data so that it doesn’t have to be fetched from the main memory. That area of memory is shared by all of the virtual machines running on a server. Data stored there by one user will be overwritten if another process needs the space.
In this case they focused on the last-level cache, a form of memory that saves processing time by temporarily storing data so that it doesn’t have to be fetched from the main memory. That area of memory is shared by all of the virtual machines running on a server. Data stored there by one user will be overwritten if another process needs the space.
If a process needs to grab something from or write something to the last-level cache and it takes longer than normal, that means another program is also accessing the cache at the same time. By observing this give-and-take, the researchers were able to deduce how much of the cache was being used by each operation. That turned out to be an important clue to what kind of data was being processed.
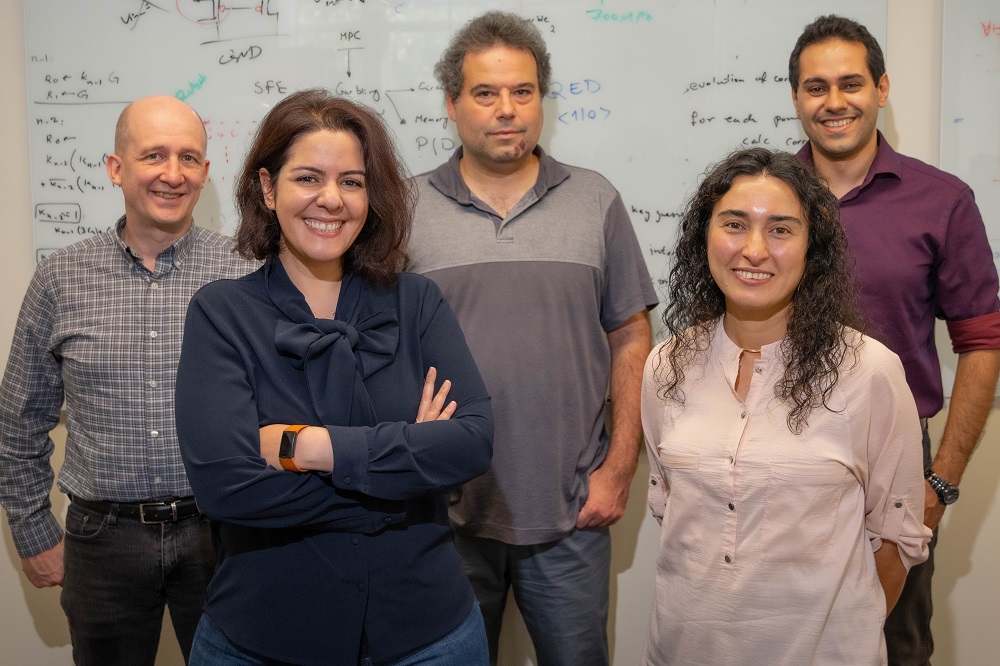
With enough observations, and the application of clever statistics, patterns in the memory usage emerged. Sunar and Eisenbarth were able to determine when they were watching the RSA key being processed. Like safecrackers carefully listening to the sound of the tumblers in the lock, they parsed out the code, digit by digit. “It’s like trying to hear a whisper in a train station,” explains Mehmet Inci, a PhD candidate who worked with Sunar and Eisenbarth on the project. If the whisper is repeated, an eavesdropper can pick up different pieces of whatever’s said each time.
The virtual machine the team monitored was one that they, themselves, had installed on the server. In fact, for the attack to work, they had to find a way to co-locate two machines, the attacker and the victim, on the same server — no small feat since machines are assigned to servers randomly to make it all but impossible for malicious parties to co-locate their machines with particular targets.
A team at the University of California San Diego and MIT first showed that co-location was possible in 2009 by making assumptions about where a server might be placed and then deploying large numbers of machines until two popped up on the same server. The WPI team devised a new co-location technique that makes use of characteristics of the last-level cache.
Leaks Beyond the Cloud
After the researchers revealed the vulnerability they’d uncovered, Amazon issued an update to its cryptographic libraries intended to fix the problem. They also pointed out that it would be difficult for less sophisticated and less diligent users to duplicate what the WPI team had accomplished. Eisenbarth agrees: “This is not an easy attack to perform,” he says.
Still, he notes, even with the software patch, “the underlying mechanisms we used are still in place.” And, since computer users are often reluctant to install patches, fearing they will disrupt their computers (about half of Amazon AWS users are still running outdated libraries), the door the WPI team walked through is far from closed.
But the other issue is that computers are always going to leak some information. With a $500,000 NSF award, Eisenbarth and Sunar have been studying such leakage in the cloud in a project called RAIN. Their work demonstrates the need for constant vigilance in the cloud to find leaks and plug them before torrents of secrets are lost. And it isn’t just a problem for companies that trust their computing to Amazon’s cloud. “Whether you know it or not, you’re already using a cloud service provider,” says Sunar. Anyone using Dropbox or Evernote to store files or Netflix to watch movies is putting their data in the cloud, and it might be stolen if security breaks down.
And it’s not just the cloud that leaks. Recently, the Vernam Group received another $500,000 NSF grant for MIST, a project to identify vulnerabilities on mobile platforms, such as smartphones. Malicious apps, perhaps in the guise of something benign like a game, can gather information about the processes running on a phone to access information about the user, for example, tracking the user’s location or capturing credit card numbers. The team hopes to develop ways to manage the processes differently so they don’t leak information, and to provide tools app developers can use to prevent leakage.
Attacks don’t have to be remote, of course, which is where the work with the oscilloscope comes in. A growing number of devices can be physically accessed by people with a reason to hack them (the way some people have tried to steal cable service for years). Figure out what a chip is doing, and one might be able to steal money from a smart card. Hack a car’s computer, and one can gain access to services from satellite radio.






 In this case they focused on the last-level cache, a form of memory that saves processing time by temporarily storing data so that it doesn’t have to be fetched from the main memory. That area of memory is shared by all of the virtual machines running on a server. Data stored there by one user will be overwritten if another process needs the space.
In this case they focused on the last-level cache, a form of memory that saves processing time by temporarily storing data so that it doesn’t have to be fetched from the main memory. That area of memory is shared by all of the virtual machines running on a server. Data stored there by one user will be overwritten if another process needs the space. Another Vernam Group project may make at least some data safer. With a $275,000 NSF grant, Sunar is working with Jeffrey Hoffstein and Joseph Silverman, mathematics professors at Brown University, to investigate new methods for achieving fully homomorphic encryption. This cryptographic technique makes is possible to send data in encrypted form to another computer for processing. The other computer performs its computations and returns an answer, also encrypted, though the other computer never “sees” the actual data.
Another Vernam Group project may make at least some data safer. With a $275,000 NSF grant, Sunar is working with Jeffrey Hoffstein and Joseph Silverman, mathematics professors at Brown University, to investigate new methods for achieving fully homomorphic encryption. This cryptographic technique makes is possible to send data in encrypted form to another computer for processing. The other computer performs its computations and returns an answer, also encrypted, though the other computer never “sees” the actual data.