Worcester, Mass. — An electrical and computer engineer at Worcester Polytechnic Institute (WPI) has received a prestigious CAREER award from the National Science Foundation (NSF) to develop a second line of cyber defense to keep intelligent systems operating safely and effectively even when hacked. The new research focuses not on keeping cyber criminals out of systems like autonomous cars, smart buildings, and robots, but on minimizing the damage they can do if they get in.
Andrew Clark, assistant professor of Electrical & Computer Engineering, is using the five-year $500,000 CAREER Award to build algorithms and use machine learning that can identify and filter out erroneous information created when a hacker breaches a system’s typical first-line security measures, like firewalls, firmware protections, and automatic bug fixes.
“It’s not enough to try to keep hackers out,” said Clark, who was awarded tenure and promoted to associate professor this year. “A smart system needs to keep working properly no matter what a hacker is telling it to do. Having a double layer of security to protect people using autonomous cars, working with robots, or living in smart homes is key to allowing consumers to trust these systems enough to actually adopt and use them.”
Clark’s cybersecurity research will apply to numerous smart systems, as well as the Internet of Things (IoT), along with industrial and personal robots, enabling them to fend off rogue instructions that could cause them to, for instance, harm humans or damage a manufacturing line.
“If a hacker attacks an industrial robot working in a large manufacturing plant and tells that machine to delete product designs, takes machines offline, or introduces defects or trojans, that’s a severe risk,” said Clark. “This is about stopping any damage from being done, whether the system is a robot, an autonomous car, or a smart air-conditioning system.”
Clark’s algorithms use estimation theory, a form of statistics used to give a value to incoming data, and control theory, which governs machine systems to keep them functioning as needed. Clark also is using planning theory, which focuses on using a hierarchy of plans to attain specific goals, to enable a system to satisfy its objective, such as driving safely down the highway, despite interference from hackers.
Using these algorithms, the researcher is working on two different levels of security.
At an initial level, Clark’s work is focused on selecting paths or making decisions with the least predictable risk. For example, a driverless car would choose a route between Point A and Point B that has less pedestrian and vehicular traffic, minimizing risk should the car’s system be hacked, or a search-and-rescue robot would choose the safest and most efficient path through a damaged building to reach a series of targets, with or without an adversary trying to hack in and stop it.
Clark’s second level of security focuses on algorithms that would enable the majority of a vehicle’s sensors to override erroneous information coming from a hacked sensor. For example, a hacker who gained access to an autonomous vehicle could try to crash the car by making one sensor show that an object was much farther away than it really was; Clark’s algorithms could override that false sensor by directing the car to discount information that doesn’t conform to the majority of its sensors, enabling it to keep a safe distance from the object.
Clark has created game theory models that capture the interaction between the system and the attacker, showing how the system reacts to differing information, what actions it can take to continue operating safely, and how those actions affect the entire system. “It lets you make predictions about how secure the system will be under different kinds of attacks, and it allows you to analyze your approach and deduce the hacker’s capabilities,” he added.
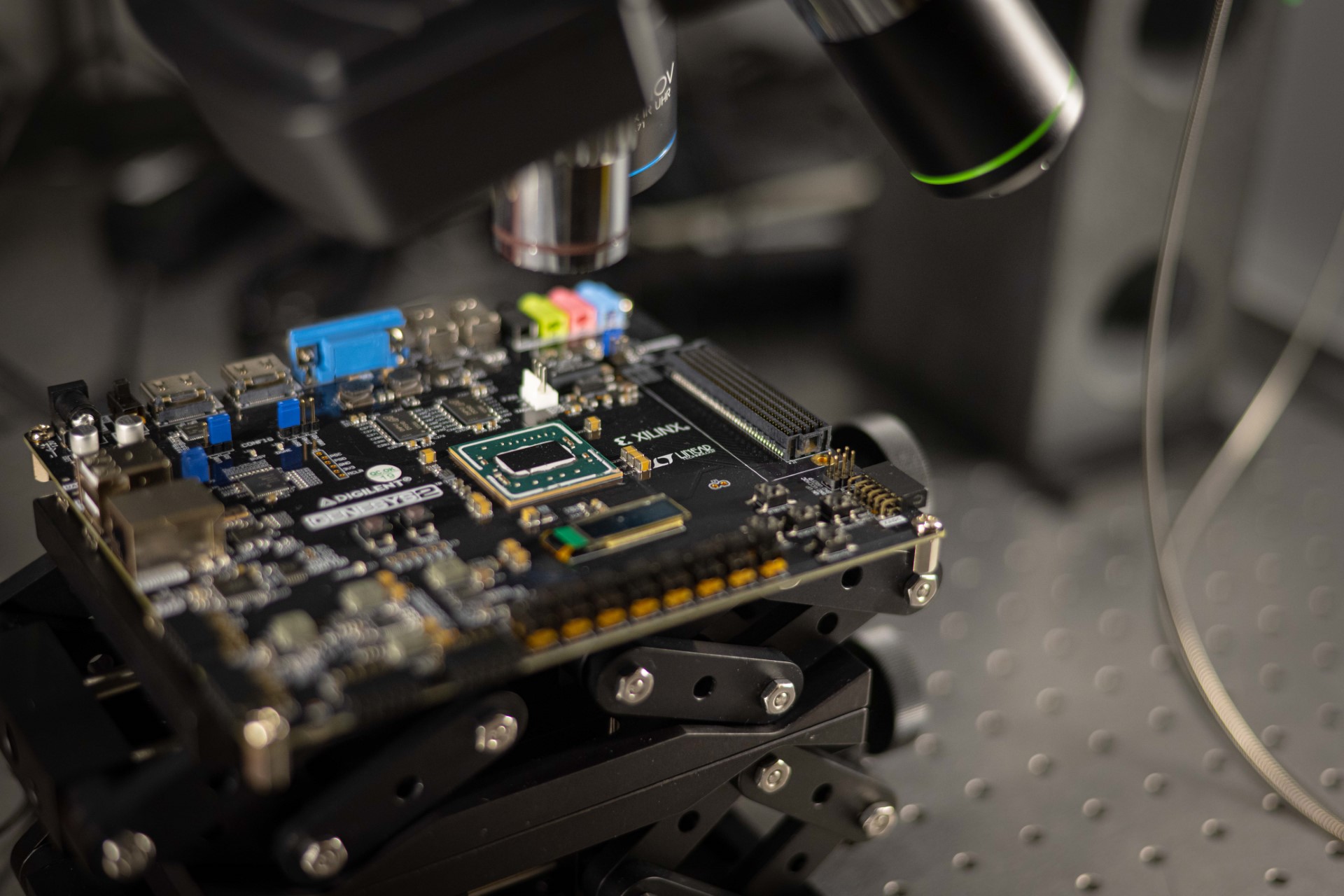
Clark has used his defense algorithms to successfully enable wheeled robots to safely navigate through his lab while its sensor feed has been compromised by a hacker. A research student is working on protecting smart home systems, materials and manufacturing; cyber, data, and security systems.