A cyber defense software program developed by a WPI professor is one of only eight technologies funded this year by the Department of Homeland Security (DHS). Craig Shue, assistant professor of computer science, has been awarded a three-year, $350,000 DHS grant to continue his work on a program that distinguishes between user-generated information and stealthy automated malware applications to help prevent attacks on individual computers from spreading through a company’s network system.
“Companies have increasingly complex relationships, including working with more business partners like delivery services, payment collectors, and other outside vendors who can inadvertently open the door to attack,” said Shue. “Attackers find the weakest point of entry to gain access to information, and often that point is within a company’s network ecosystem.”
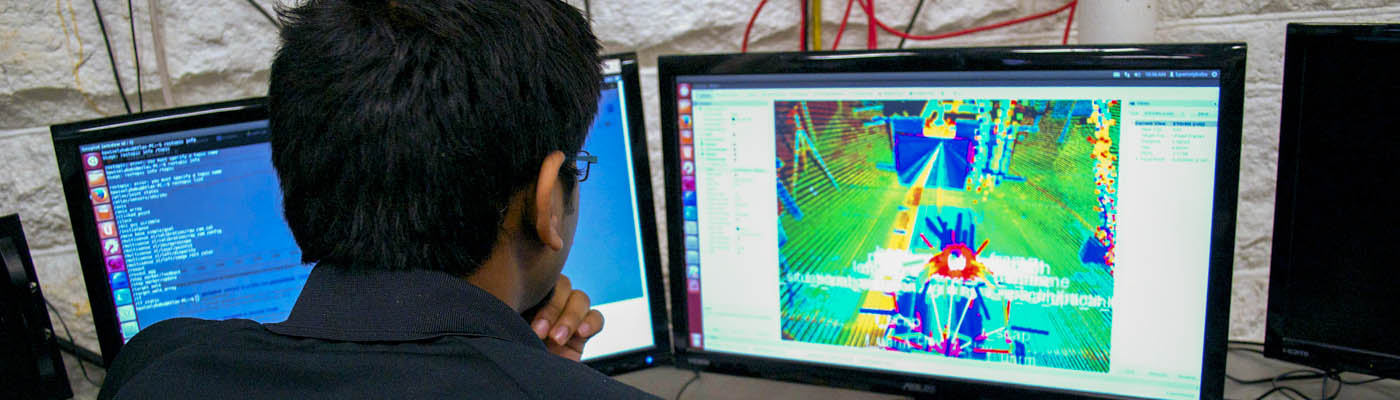
More than a simple firewall around a network’s perimeter, Shue’s software allows corporate networks to understand the purpose behind data transmitted into the network. The software can identify human interaction on a computer, such as a user typing a message or opening a website, therefore letting the system know the action is legitimate. Malware or spam programs have no contact with a computer’s hardware when attempting to send data throughout a network, and thus would be flagged as deceptive.
According to Shue, “Network operators can be overwhelmed by the volume of data on their networks. They must act like detectives and manually reconstruct events to find threats. A perimeter defense won’t see something happening inside a network. Our approach installs software on each computer in a network that asks a centralized coordinator for permission before enabling any action, so we’re basically putting a perimeter defense around each computer.”
Shue created the software with prior funding from the National Science Foundation. Under the DHS grant, he and his team will finalize the program and make it available for industry use. In addition to the novel approach to setting up a defense on individual computers, Shue is working to make his software affordable for businesses of any size. “In today’s highly connected world, attackers are targeting even small businesses, so our protections must be affordable for everyone,” says Shue.
Shue’s work was identified by the DHS Transition to Practice Program as a product that “can have tremendous potential for commercial applications throughout the nation, enhance the competitiveness of individual small businesses, as well as expand areas of exploration and cooperation for all non-federal partners.” In collaboration with DHS, Shue will demonstrate his software at a series of events to identify a test market partner with the goal of commercializing the product within the next two years.